Network Tokenization: The Complete Guide to Secure Payment Optimization

Network Tokenization: The Complete Guide to Secure Payment Optimization
In an era where data breaches make headlines weekly and payment fraud costs businesses billions annually, network tokenization has emerged as a critical security technology that does more than just protect sensitive data—it actively improves payment performance and boosts revenue. Unlike traditional tokenization methods, network tokens are issued directly by card networks (Visa, Mastercard, American Express, Discover), providing unique advantages that forward-thinking merchants are leveraging to gain competitive advantage.
This comprehensive guide explores everything you need to know about network tokenization in 2026: how it works, why it outperforms traditional vault-based tokenization, and how to implement it for maximum security and conversion optimization.
What Is Network Tokenization?
Network tokenization replaces sensitive primary account numbers (PANs)—the 16-digit card numbers printed on physical cards—with unique digital tokens issued and managed directly by card networks. These tokens are specific to both the merchant and the device or channel, meaning a stolen token is useless anywhere else.
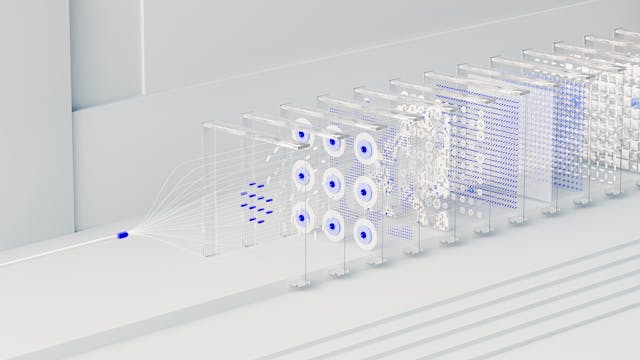
How Network Tokenization Works
The network tokenization process involves several sophisticated steps:
1. Token Request: When a customer enters their card details for the first time, the merchant’s payment system sends a tokenization request to their payment orchestration platform or directly to the card network’s token service provider (TSP).
2. Token Generation: The card network generates a unique token—a randomized 16-digit number that follows the same format as a real card number but has no intrinsic value if compromised. This token is cryptographically bound to the specific merchant and cannot be used elsewhere.
3. Token Provisioning: The token is securely provisioned to the merchant’s systems, replacing the actual PAN for all future transactions. The original card data is never stored on merchant servers.
4. Transaction Processing: When processing subsequent payments, the merchant uses the token instead of the real card number. The payment orchestration layer handles the translation between token and PAN, ensuring the actual card data remains protected throughout the transaction lifecycle.
5. Lifecycle Management: The card network continuously manages the token, automatically updating it when the underlying physical card is replaced, expired, or compromised—eliminating the need for customers to re-enter payment details.
Network Tokens vs. Traditional Tokens
While both network and traditional (gateway/processor) tokenization replace sensitive card data with non-sensitive equivalents, critical differences impact security, performance, and operational efficiency:
The Business Case for Network Tokenization
Network tokenization delivers measurable business benefits that extend far beyond basic compliance requirements. Understanding these advantages helps build the investment case for implementation.
Higher Authorization Rates
The most compelling business benefit of network tokenization is improved transaction approval rates. Studies consistently show that transactions processed with network tokens achieve 2-6% higher authorization rates compared to traditional PAN-based transactions.
Why Network Tokens Perform Better:
- Issuer Confidence: Banks and issuers trust network tokens more because they’re cryptographically verified by card networks, reducing false decline rates
- Fresh Credential Status: Network tokens represent the most up-to-date card information, reducing declines from expired or replaced cards
- Reduced Fraud Scoring: The enhanced security of network tokens often results in lower risk scores from issuer fraud systems
- Device Binding: Tokens can be bound to specific devices, providing additional authentication signals that improve approval odds
Revenue Impact Calculation:
For a merchant processing $50 million annually with an average authorization rate of 85%:
- Current approved volume: $42.5 million
- With 3% improvement (88% authorization): $44 million
- Additional annual revenue: $1.5 million
Automatic Card-on-File Updates
One of the most operationally valuable features of network tokenization is automatic lifecycle management. When a customer’s physical card is replaced—whether due to expiration, loss, theft, or compromise—the network token is automatically updated without any action required from the merchant or customer.
The Business Impact:
- Reduced Involuntary Churn: Card expirations account for 15-20% of SaaS churn. Network tokens eliminate this failure mode entirely.
- Improved Customer Experience: Customers never need to update payment details when they receive new cards
- Operational Efficiency: Support teams spend less time helping customers update expired cards
- Uninterrupted Subscriptions: Recurring billing continues seamlessly through card replacements
Real-world data shows that merchants using network tokenization experience 40-60% fewer payment failures due to expired or replaced cards compared to those relying on traditional card storage methods.
Enhanced Security and Fraud Prevention
Network tokenization provides multiple layers of security that dramatically reduce fraud risk:
Cryptographic Security:
- Tokens are generated using cryptographic algorithms that make reverse-engineering practically impossible
- Each token is unique to the merchant-device combination, limiting exposure if breached
- Dynamic data elements (cryptograms) can be included with each transaction, creating one-time-use authentication codes
Domain Restrictions:
- Network tokens can be restricted to specific merchant IDs, rendering stolen tokens useless if used elsewhere
- Channel restrictions prevent token misuse across different transaction types (e-commerce vs. in-store)
Fraud Liability Shift:
- Transactions using network tokens with 3D Secure authentication benefit from liability shift protection
- Merchants may see reduced chargeback rates and lower fraud-related losses
- Some card networks offer preferential interchange rates for tokenized transactions
Reduced PCI DSS Scope
Network tokenization significantly simplifies PCI compliance requirements:
- SAQ A Eligibility: Merchants using fully hosted tokenization solutions may qualify for the simplest PCI Self-Assessment Questionnaire (SAQ A), reducing compliance costs and audit complexity
- Reduced Data Environment: Since actual card data never touches merchant systems, the cardholder data environment (CDE) is minimized
- Lower Compliance Costs: Simplified assessments mean reduced auditor fees and internal compliance resource requirements
- Decreased Breach Risk: With no actual card data stored, the impact of a security breach is dramatically reduced
Implementing Network Tokenization: Technical Considerations
Successful network tokenization implementation requires careful technical planning and integration.
Integration Approaches
Direct-to-Network Integration:
Large enterprises with substantial technical resources may integrate directly with card network token services:
- Visa Token Service (VTS)
- Mastercard Digital Enablement Service (MDES)
- American Express SafeKey
- Discover Digital Exchange (DDX)
Advantages:
- Maximum control over tokenization processes
- Direct relationship with card networks
- Potential cost savings at high volumes
Challenges:
- Complex integration requiring specialized expertise
- Separate implementations for each card network
- Ongoing maintenance and certification requirements
- Significant development and testing resources
Payment Orchestration Platform Integration:
Most merchants achieve network tokenization through their payment orchestration platform:
Advantages:
- Single integration provides access to multiple card networks
- Simplified technical implementation
- Automatic updates as tokenization standards evolve
- Unified reporting and management across networks
- Built-in failover and redundancy
Considerations:
- Platform fees for tokenization services
- Dependency on provider’s roadmap and capabilities
- Ensure platform supports your required use cases
Token Provisioning Workflows
Initial Card Capture:
Modern implementations support multiple token provisioning methods:
1. Real-Time Tokenization: Card data is tokenized immediately upon entry, with the token returned for merchant storage while the actual PAN is discarded
2. Click-to-Pay Integration: Customers can select stored payment methods from their digital wallets, automatically provisioning network tokens
3. Issuer Wallet Integration: Direct integration with bank-provided digital wallets for seamless token provisioning
Stored Credential Compliance:
Network tokenization must comply with card network stored credential frameworks:
- Initial Storage: First-time storage requires explicit cardholder consent
- Subsequent Transactions: Merchant-initiated transactions must include appropriate indicators
- Transaction Types: Clear distinction between customer-initiated and merchant-initiated transactions
- Recurring Indicators: Proper flagging of subscription vs. one-off transactions
Multi-Provider Token Management
For merchants using multiple payment providers, token portability becomes critical:
The Challenge:
Traditional tokens are locked to specific processors. If you switch from Provider A to Provider B, all stored tokens become useless, requiring customers to re-enter payment details.
The Network Token Solution:
Network tokens are portable across processors because they’re issued by card networks, not payment providers. When switching processors, the same network tokens continue working seamlessly.
Implementation Best Practices:
- Store network tokens in a provider-agnostic format
- Maintain mapping between internal customer IDs and network tokens
- Implement token lifecycle event handling (updates, deletions, suspensions)
- Ensure consistent token usage across all integrated providers
Advanced Network Tokenization Strategies
Sophisticated implementations leverage advanced tokenization features for competitive advantage.
Device Binding and Authentication
Network tokens can be cryptographically bound to specific devices, creating an additional authentication factor:
Use Cases:
- Mobile Apps: Tokens bound to specific devices reduce fraud while enabling frictionless mobile checkout
- Browser Fingerprinting: Web-based tokens can incorporate device characteristics for risk scoring
- IoT Payments: Smart device payments use device-bound tokens to prevent unauthorized usage
Implementation:
- Device binding requires integration with device identification services
- Balance security with user experience—excessive binding can create friction
- Provide fallback authentication when devices change
Dynamic Data Elements (Cryptograms)
Advanced network tokenization includes dynamic cryptograms—one-time-use authentication codes generated for each transaction:
Benefits:
- Cryptograms prove token possession, preventing replay attacks
- Even if a token is intercepted, it cannot be reused without the dynamic cryptogram
- Additional authentication layer without customer friction
Use Cases:
- High-value transactions requiring enhanced authentication
- Transactions from new devices or locations
- First-time transactions with stored credentials
Multi-Token Strategies
Sophisticated merchants may maintain multiple network tokens for the same underlying card:
Channel-Specific Tokens:
- Separate tokens for e-commerce, mobile app, and in-store payments
- Device-specific tokens for high-value customers
- Geographic restrictions based on transaction location
Use Case-Specific Tokens:
- Subscription tokens optimized for recurring billing
- One-click checkout tokens for returning customers
- Guest checkout tokens with shorter lifecycles
Measuring Network Tokenization Success
Effective implementation requires comprehensive measurement and optimization.
Key Performance Indicators
Authorization Rate Improvements:
- Baseline authorization rates before tokenization
- Segment analysis by card network, transaction type, and geography
- A/B testing of tokenized vs. non-tokenized transaction flows
- Long-term trend analysis as token adoption increases
Operational Metrics:
- Percentage of stored credentials using network tokens
- Card update rates (should approach zero for network tokens)
- Customer support tickets related to expired cards
- Time saved in payment operations
Security and Fraud Metrics:
- Fraud rates for tokenized vs. non-tokenized transactions
- Chargeback rates and reason code analysis
- PCI compliance audit findings and remediation costs
- Breach risk assessment scores
Benchmarking and Optimization
Industry Benchmarks:
- Top-performing merchants achieve 80-90% network token adoption for stored credentials
- Average authorization rate improvements range from 2-6%
- Fraud rates typically decrease 25-40% for tokenized transactions
Continuous Optimization:
- Regular analysis of token performance by card network
- Monitoring for new tokenization features and capabilities
- A/B testing of token provisioning workflows
- Customer feedback analysis on payment experience
The Future of Network Tokenization
The network tokenization landscape continues evolving rapidly, with several trends shaping its future.
Click-to-Pay and Universal Wallets
Card networks are pushing Click-to-Pay standards that leverage network tokens for universal digital wallet compatibility:
- Merchant Benefits: Single integration supports multiple digital wallets
- Customer Experience: Consistent checkout experience across merchants
- Security: Universal implementation of network tokenization best practices
Biometric Authentication Integration
Network tokens are increasingly combined with biometric authentication:
- Fingerprint/Face Recognition: Device-based biometrics combined with network tokens
- Behavioral Biometrics: Transaction patterns analyzed alongside token usage
- Step-Up Authentication: Risk-based biometric challenges for high-value transactions
Real-Time Payment Integration
As real-time payment networks expand globally, network tokenization is extending beyond card payments:
- Account-to-Account Transfers: Tokenization of bank account details
- Cross-Border Real-Time: Tokenized credentials for international instant payments
- Request-to-Pay: Secure tokenized payment requests
Implementing Network Tokenization: Step-by-Step
For merchants ready to implement network tokenization, here’s a practical roadmap:
Phase 1: Assessment and Planning (2-4 weeks)
1. Current State Audit
– Inventory existing stored payment credentials
– Analyze current authorization rates by card network
– Document current tokenization approach (if any)
– Assess PCI compliance scope and costs
2. Requirements Definition
– Identify supported card networks (recommend all major networks)
– Define use cases (one-time, recurring, subscription, etc.)
– Determine integration approach (direct vs. orchestration platform)
– Establish success metrics and KPIs
3. Provider Selection
– Evaluate payment orchestration platforms with network tokenization
– Assess technical capabilities and integration complexity
– Compare pricing models (per-token, per-transaction, flat fee)
– Review security certifications and compliance attestations
Phase 2: Technical Integration (4-8 weeks)
1. Development Environment Setup
– Configure sandbox/test environments
– Establish connectivity with token service providers
– Implement token provisioning workflows
– Build token lifecycle management (updates, deletions)
2. Integration Development
– Modify checkout flows for real-time tokenization
– Update stored credential management systems
– Implement token retrieval for repeat transactions
– Build error handling and fallback processes
3. Testing and Validation
– Functional testing of token provisioning
– Authorization rate testing (tokenized vs. non-tokenized)
– Security testing and penetration testing
– Compliance validation for stored credential frameworks
Phase 3: Deployment and Optimization (2-4 weeks)
1. Gradual Rollout
– Begin with specific customer segments or transaction types
– Monitor performance metrics closely
– Address any integration issues
– Gather customer feedback
2. Full Production Deployment
– Expand to all eligible transactions
– Migrate existing stored credentials to network tokens
– Decommission legacy tokenization systems
– Update operational procedures and documentation
3. Continuous Optimization
– Monitor KPIs and benchmark performance
– A/B test optimization strategies
– Stay current with evolving tokenization standards
– Regular security assessments and updates
Conclusion: The Tokenization Imperative
Network tokenization has evolved from a niche security feature to a foundational payment infrastructure component that directly impacts revenue, customer experience, and operational efficiency. The combination of enhanced security, higher authorization rates, automatic credential updates, and reduced compliance burden creates a compelling value proposition for merchants of all sizes.
As the payment ecosystem continues evolving—with expanding digital wallets, real-time payments, and increasingly sophisticated fraud threats—network tokenization provides the secure, flexible foundation modern commerce requires. Merchants who haven’t yet implemented network tokenization are leaving money on the table through lower authorization rates, higher operational costs, and unnecessary compliance burden.
The question is no longer whether to implement network tokenization, but how quickly you can deploy it to capture the benefits. In an increasingly competitive digital economy, optimized payment infrastructure isn’t just about processing transactions—it’s about maximizing every revenue opportunity while protecting your business and customers from evolving threats.
Ready to implement network tokenization? Contact Paymid to learn how our payment orchestration platform provides enterprise-grade network tokenization with seamless integration, automatic lifecycle management, and comprehensive analytics to optimize your payment performance.
—
Paymid’s payment orchestration platform includes built-in network tokenization across all major card networks, providing higher authorization rates, enhanced security, and reduced PCI scope without complex technical integration. Process payments with confidence knowing your customers’ credentials are protected by industry-leading tokenization technology.