3D Secure 2.0 Orchestration: Maximizing Security Without Killing Conversions

Security and conversions have always been at odds in online payments. The more security layers you add, the more friction customers experience—and the more likely they are to abandon their purchase. 3D Secure 2.0 (3DS2) promised to change this equation, offering stronger fraud protection with less friction. But the reality? Most merchants are still struggling to find the right balance.
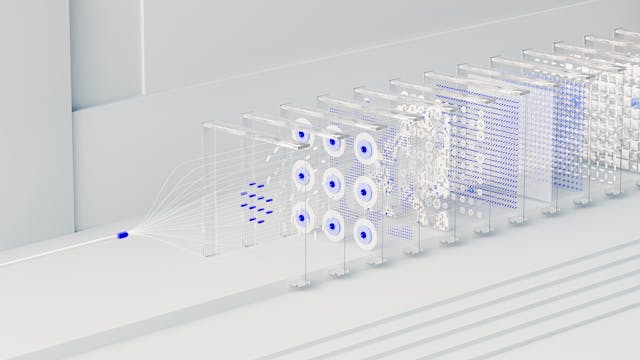
Enter 3D Secure orchestration: the intelligent approach to authentication that maximizes security without devastating your conversion rates. By leveraging smart routing, risk-based authentication, and strategic exemption rules, leading merchants are achieving both lower fraud rates AND higher approval rates.
In this comprehensive guide, we’ll explore how 3D Secure 2.0 works, why orchestration matters, and how to implement a strategy that protects your business while keeping customers happy.
What is 3D Secure 2.0?
3D Secure 2.0 is the updated authentication protocol designed to reduce fraud in card-not-present transactions while improving the customer experience over its predecessor (3DS1). Developed by EMVCo with participation from major card networks (Visa, Mastercard, American Express, Discover, JCB), 3DS2 addresses the primary complaints about the original 3D Secure.
3DS1 vs 3DS2: Key Differences
| Feature | 3D Secure 1.0 | 3D Secure 2.0 |
|---|---|---|
| Authentication Flow | Always redirects to bank page | Risk-based, often frictionless |
| Mobile Experience | Poor—breaks in-app flows | Native mobile SDK support |
| Data Sharing | Limited (5-10 data points) | Rich (100+ data points) |
| Customer Friction | High—passwords, codes | Low—often invisible |
| Fraud Liability Shift | Yes | Yes, with exemptions |
| Checkout Drop-off | 20-30% | 2-5% |
How 3DS2 Works
Instead of forcing every customer through an authentication challenge, 3DS2 uses risk-based authentication:
- Data Collection: The merchant’s system collects rich transaction and device data (100+ data points)
- Risk Assessment: The issuer’s access control server (ACS) analyzes the data using ML models
- Decision:
- Low risk → Frictionless flow (no customer interaction)
- High risk → Challenge flow (customer authenticates)
- Authentication: If challenged, customer verifies via biometrics, SMS, banking app, or other methods
- Result: Issuer returns authentication result; merchant proceeds with authorization
Why 3DS2 Alone Isn’t Enough
While 3DS2 is a significant improvement, simply enabling it without strategy creates new problems:
The Challenge Rate Problem
Even with 3DS2, challenged transactions convert 20-40% lower than frictionless ones. Poor implementation can result in:
- 60-80% challenge rates (too many customers forced to authenticate)
- Inconsistent experiences across card issuers
- Mobile checkout abandonment due to authentication friction
- Revenue loss that exceeds fraud savings
The Exemption Confusion
Strong Customer Authentication (SCA) regulations allow exemptions for:
- Low-value transactions (under €30)
- Merchant-initiated transactions
- Subscription renewals
- Low-risk transactions (TRA exemption)
But navigating these exemptions while maintaining compliance requires sophisticated logic—and getting it wrong means either unnecessary friction or regulatory penalties.
The Multi-Provider Complexity
When using multiple payment providers, 3DS2 implementation becomes even more complex:
- Different providers support different 3DS2 versions
- Exemption rules vary by provider
- Challenge flows look different across providers
- Data requirements differ between implementations
What is 3D Secure Orchestration?
3D Secure orchestration solves these challenges by intelligently managing authentication across multiple dimensions:
1. Risk-Based Routing
Route transactions to the optimal path based on risk assessment:
- Low risk transactions: Request exemption, skip 3DS entirely
- Medium risk: Frictionless 3DS2 (data sharing only)
- High risk: Full challenge flow
- Suspicious: Block or manual review
2. Provider Optimization
Choose the best provider for each transaction considering:
- Which provider has the best 3DS2 approval rate for this card type/country
- Which provider supports the optimal exemption for this transaction
- Real-time provider performance (some providers’ ACS systems perform better)
- Cost optimization (3DS2 fees vary by provider)
3. Smart Exemption Management
Automatically apply for the most appropriate exemption:
- Low Value Exemption (LVE) for transactions under €30
- Transaction Risk Analysis (TRA) exemption based on fraud rates
- Merchant-Initiated Transaction (MIT) exemption for subscriptions
- Subscription exemption for recurring payments
4. Challenge Flow Optimization
When challenges are unavoidable, optimize the experience:
- Native mobile app authentication instead of browser redirects
- Biometric authentication (FaceID, TouchID) when available
- SMS/Email fallback for customers without banking apps
- Seamless iframe integration to avoid full-page redirects
Benefits of 3DS2 Orchestration
1. Reduced Checkout Friction
Strategic orchestration can reduce challenge rates from 40-60% to 5-15%, significantly improving conversions:
- Frictionless authentication for 85-95% of transactions
- Streamlined challenge flows for the remainder
- Mobile-optimized experiences
2. Lower Fraud Rates
Better risk assessment means:
- Fraudulent transactions caught before authorization
- Fewer chargebacks (liability shift to issuer)
- Reduced manual review costs
- Lower fraud-related operational overhead
3. Compliance Optimization
Navigate SCA requirements strategically:
- Apply exemptions where allowed
- Maintain audit trails for regulatory reporting
- Adapt to changing regulations automatically
- Avoid penalties for non-compliance
4. Improved Authorization Rates
Contrary to intuition, proper 3DS2 implementation can IMPROVE authorization rates:
- Issuers trust authenticated transactions more
- Liability shift encourages issuer approval
- Rich data improves risk decisions
- Reduced false declines
Key Strategies for 3DS2 Orchestration
Strategy 1: Intelligent Exemption Requesting
Don’t default to 3DS for every transaction. Request exemptions strategically:
TRA (Transaction Risk Analysis) Exemption:
Available when:
- Fraud rate is below threshold (0.13% for transactions under €100, 0.06% for €100-€250, 0.01% for €250+)
- Transaction fits acquirer’s risk parameters
Low Value Exemption (LVE):
- Transactions under €30
- Limited to 5 consecutive exempt transactions or €100 cumulative
Subscription Exemptions:
- First payment authenticated, subsequent payments exempt
- Merchant-initiated transactions (MIT)
Strategy 2: Dynamic 3DS Decisioning
Use machine learning to decide when to trigger 3DS:
IF fraud_score < 20 AND customer_trust_score > 80:
REQUEST exemption
ELIF fraud_score < 40:
FRICTIONLESS_3DS
ELIF fraud_score < 70:
CHALLENGE_3DS
ELSE:
BLOCK or MANUAL_REVIEW
Strategy 3: Provider-Specific Optimization
Not all 3DS2 implementations are equal. Optimize by:
- Version support: Prefer providers using 3DS2.2 (latest) over 2.1
- Decoupled authentication: Enable app-to-app authentication for mobile
- 3DS method: Use device fingerprinting to increase frictionless rates
- Exemption success rates: Route to providers with higher exemption approval
Strategy 4: Mobile-First Design
Mobile transactions require special attention:
- Use native SDKs instead of browser-based flows
- Support biometric authentication (FaceID, fingerprint)
- Implement app-to-app authentication with banking apps
- Optimize iframe sizing for mobile screens
Implementation Best Practices
Phase 1: Assessment
Before implementing 3DS2 orchestration:
- Audit current fraud rates: Calculate your current fraud rate by transaction value band
- Review chargeback data: Identify patterns in fraud-related chargebacks
- Analyze current conversion funnel: Baseline your checkout abandonment rates
- Map transaction types: Categorize transactions by value, channel, customer type
Phase 2: Provider Selection
Evaluate payment providers on:
- 3DS2 version support (2.1 vs 2.2)
- ACS (Access Control Server) performance and uptime
- Exemption request capabilities
- Mobile SDK quality
- Reporting and analytics
- Cost structure (authentication fees, exemption fees)
Phase 3: Gradual Rollout
Implement in stages:
- Week 1-2: Enable 3DS2 for 10% of traffic, monitor closely
- Week 3-4: Increase to 50%, optimize exemption rules
- Week 5-6: Full rollout with exemption optimization
- Ongoing: Continuous monitoring and optimization
Phase 4: Optimization
Continuously improve:
- A/B test exemption strategies
- Monitor challenge rates by issuer
- Track authorization rate changes
- Optimize risk scoring thresholds
Measuring 3DS2 Orchestration Success
Key Performance Indicators
| Metric | Baseline (No 3DS2) | Target (With Orchestration) |
|---|---|---|
| Fraud Rate | Current rate | -30% to -50% |
| Challenge Rate | N/A | <15% |
| Challenge Completion Rate | N/A | >85% |
| Authorization Rate | Current rate | +2% to +5% |
| Checkout Abandonment | Current rate | No increase |
| Chargeback Rate | Current rate | -40% to -60% |
Analytics to Track
Set up monitoring for:
- Exemption success rates by type (TRA, LVE, MIT)
- Challenge rates by issuer and card type
- Frictionless authentication rates
- Authorization rates with vs. without 3DS
- Mobile vs. desktop performance differences
- Revenue impact (saved fraud losses vs. conversion impact)
Common 3DS2 Orchestration Mistakes
Mistake 1: Defaulting to 3DS for Everyone
Wrong: Enabling 3DS for 100% of transactions
Right: Strategic exemption requesting based on risk
Mistake 2: Ignoring Mobile Experience
Wrong: Using browser-based redirects for mobile apps
Right: Native SDK implementation with app-to-app support
Mistake 3: Static Rules
Wrong: One-size-fits-all 3DS rules
Right: Dynamic risk-based decisioning with ML
Mistake 4: Not Monitoring Issuer Performance
Wrong: Treating all issuers the same
Right: Routing around issuers with poor 3DS performance
Mistake 5: Poor Fallback Handling
Wrong: Failing entirely if 3DS fails
Right: Graceful fallback to exemptions or alternative providers
Future of 3D Secure Orchestration
Emerging Trends
AI-Powered Risk Scoring:
Advanced machine learning models analyzing:
- Behavioral biometrics
- Device intelligence
- Transaction patterns
- Network effects across merchants
Click-to-Pay with 3DS:
Visa, Mastercard, Amex unified checkout experience with built-in 3DS2 orchestration.
Delegated Authentication:
Merchants authenticating customers directly using bank-grade security, reducing friction.
Biometric-First Authentication:
Face recognition, voice biometrics, and behavioral patterns replacing passwords and SMS codes.
Conclusion
3D Secure 2.0 doesn’t have to be a conversion killer. With intelligent orchestration, you can achieve the holy grail of payments: LESS fraud AND higher conversions.
The key is treating 3DS2 as a strategic tool rather than a compliance checkbox. By leveraging smart routing, risk-based authentication, and strategic exemptions, you can protect your business while delivering the seamless checkout experience customers expect.
Start by assessing your current state, choose providers with robust 3DS2 capabilities, and implement gradual optimization. The merchants who master 3DS2 orchestration today will have a significant competitive advantage as fraud prevention becomes increasingly critical.
Ready to implement intelligent 3DS2 orchestration? Contact Paymid to learn how our payment orchestration platform can help you balance security and conversions.